Phishing, social engineering being used to acquire data
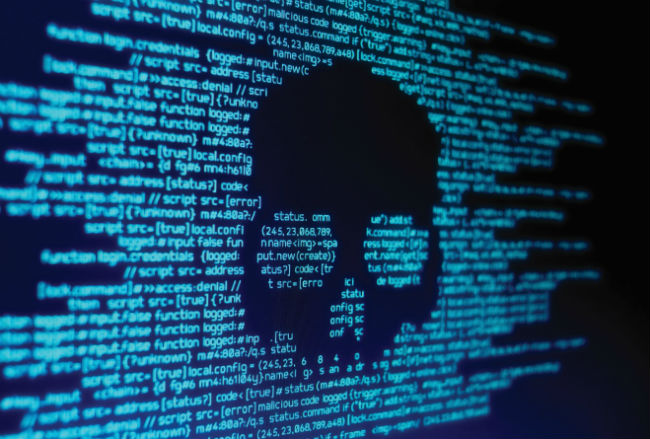
Malware. Ransomware. Phishing. Social engineering. While these words may sound like they are from science fiction, they are actually some of the methods that cybercriminals use to attack organizations’ operations — including payroll data.
“Different kinds of attacks or different kinds of breaches can happen to any company’s payroll department,” said Sangameswaran Manikkayam, manager of system engineering in Canada for security services provider Trustwave.
That payroll data is valuable because it includes employees’ personal information, such as social insurance numbers and bank account numbers, which can be used for identity theft, he said.
Trustwave’s 2018 Global Security Report ranked phishing and social engineering as the most common threats to corporate networks, at 55 per cent of all incidents.
Social engineering uses various methods of human interaction to trick people into providing confidential information. It could be a phone call or an email from someone pretending to be an employee who needs their password reset, or a payroll service provider asking for updated information.
When emails are used to do this, it is typically called phishing. The emails appear to be from a legitimate person or organization seeking financial and/or identify information.
“A cybercriminal might customize each phishing email, so that can make you fall victim to the phishing email and click on that link,” said Manikkayam.
In the United States, the Internal Revenue Service (IRS) has repeatedly warned payroll departments about phishing emails that pretend to be from a member of an organization’s executive team seeking updated employee information. They may ask for names, social security numbers, and income information, often from their W2 forms, which are similar to T4s.
“The W2 scam has emerged as one of the most dangerous and successful phishing attacks as hundreds of employers and tens of thousands of employees fell victim to the scheme in the past year,” the IRS said last fall.
Another concern is that payroll systems could become victim to malware or ransomware attacks if an unsuspecting payroll professional clicks on a link in an email or on a website, said Manikkayam.
A malware attack could install software on the payroll system that enables cybercriminals to access or destroy data.
“Cyberattacks that manipulate or destroy data can undermine trusted systems without the owner’s knowledge and have the potential to damage critical infrastructure,” said The Global State of Information Security® Survey 2018 on information security by professional services firm PwC.
The report surveyed more than 9,500 global company executives. In 2017, 30 per cent of respondents said their employee records were compromised because of a cyberattack.
A ransomware attack is a form of malware that can lead to an organization’s computer system or files being held hostage.
“Somebody clicks on an unsuspected-looking link and they download a piece of malicious code onto that machine,” said Manikkayam. “From there, the machine gets locked out so people cannot access the payroll information.”
The cybercriminal then demands payment to “unlock” the computer or the files.
Cyberattacks may come from outside or within an organization. PwC’s report estimated that 30 per cent of security incidents likely come from current employees and 26 per cent from former employees.
Cybercriminals working within an organization pose an increased threat, said Manikkayam.
“It’s more dangerous because an insider may be having increased levels of access to critical resources within the organization,” he said.
“They might know where the payroll database is stored and who has the access, so they can use social engineering to try to find out the password.”
There are a number of tools organizations can use to prevent cyberattacks. They include using up-to-date antivirus software and firewalls, applying security updates as soon as they are available, and implementing tools to scan and filter incoming email.
Other methods include limiting the number of employees with administrative privileges to computer programs, requiring complex passwords, and restricting the types of websites employees can visit.
For payroll, Manikkayam recommended having multiple security controls in place.
“It’s all about the concept of layered security, understanding how the payroll database has been configured, whether the default passwords have been changed or not. In many instances, the default database password has not been changed for a long period of time. Anyone who knows the default database password gets free access.”
Manikkayam’s concern about passwords highlights the fact that technology alone will not solve cybercrime.
“Another concern is the human factor. It remains the greatest hurdle for any kind of cybersecurity program,” he said.
A recent report on global information security from professional services firm Ernst & Young underscores the role that employees play.
“For many organizations, the most obvious point of weakness will come from an employee who is careless or fails to heed the cybersecurity guidelines,” said the report Cybersecurity regained: preparing to face cyber attacks.
“Employee awareness is also a crucial front-line defence, building cybersecurity consciousness and password discipline throughout the organization.”
The report recommends organizations implement education and awareness programs for employees.
And Manikkayam said such programming should include a number of components.
“(Employees) should find out when to change their individual password; how not to fall victim to a social engineering attack; how they should not click on a phishing email; how not to reveal sensitive information unless you are sure who the person is on the other side; and about sharing sensitive information over unencrypted channels,” he said.
Employers should run the programs regularly — possibly once a month to begin — so that employees learn to keep cybersecurity top of mind, said Manikkayam.
“Handling the human factor starts with having good security policies, good security procedures, and having periodic security awareness education for all employees in the organization. Because if you do it only once a year, the chances are that the employees might go through that and then forget it after a couple of months,” he said.
“Do a periodic phishing exercise to see whether specific departments are getting into a compromise, like they are clicking on the link, they are trying to open an attachment with a malicious file.”
In case a cybersecurity breach does occur, payroll departments should be proactively prepared with pre-written policies and procedures to deal with it, said Manikkayam.
The policies should address a range of issues.
“What are the cybersecurity incidents and what are the response methods? What are the procedures which should be followed in case of any kind of security compromise or breach on the payroll data?” he said.
“It definitely makes sense to have all of these things documented and have a training awareness session given to the first responders in case a security incident happens.”
SIDEBAR
Cybersafety strategy
The federal government has created a cybersafety guide for small and mid-size businesses. It includes the following tips:
• Use complex passwords containing letters, numbers, and symbols.
• Only visit trusted websites while using business computers or working with business information.
• Never remove or disable security safeguards, such as anti-virus software, on business networks and computers.
• Ask anyone making unusual inquiries about employees, families, or sensitive business matters to verify their identity.
• Always report suspicious activity to a supervisor.
• Do not forward potentially harmful emails. If you need to show it to a supervisor, show them your screen or print it out.
• Do not answer suspicious emails or provide confidential information requested in emails even if they appear legitimate. Contact the legitimate client or organization through another means to ask if they sent the email.
Source: Get Cyber Safe Guide for Small and Medium Businesses